DTP is pre-configured to meet most LDAP system requirements, but you may have to configure additional directory settings if the minimal LDAP configuration is unsuccessful. After changing a configuration, you should click Preview Data to verify the settings. This function does not persist data and is a useful tool for ensuring that your LDAP configuration functions as expected.
In this section:
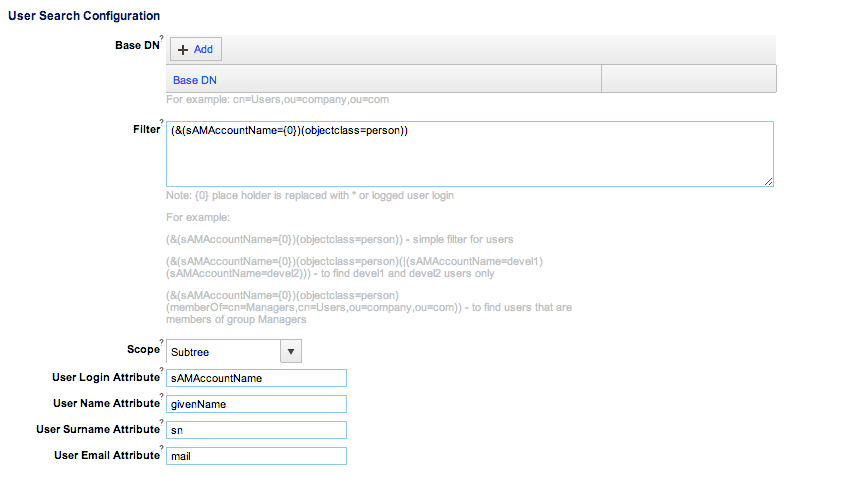
User Search Configuration
Base DN
This is the context DN where the directory objects reside. If empty, DTP will use the root DN of the directory tree. You can specify more then one base DN. This should only be configured to narrow down the users retrieved from the directory server. The following table includes examples that describe how you can filter the data retrieved from the directory server by configuring the base DN:
| Example | Configuration |
|---|---|
| No base DN set (the root DN of the directory tree is used) |
|
Entering multiple base DNs to import specific groups of users | Organizational units (ou) and domain components (dc) are used to define directory tree structures. In this example, the directory tree is organized in following way:
You can enter the following base DNs to scan users from Europe and Asia only.
|
Filter
Enter an expression in the Filter field to search on specific parameters. Searches are performed on the base DN(s) and scope specified. The following table contains examples that describe some of the ways filters can be used:
| Example | Configuration |
|---|---|
| Simple filter for users under provided base DN | (&(sAMAccountName={0})(objectclass=person)) |
| Find devel1 and devel2 users only: |
|
| Find users that are members of group Managers: |
|
Scope
Enter a value in the Scope field to define the depth and breadth of searches, e.g. Object, OneLevel, Subtree.
Attributes
User Administration queries directory objects and maps each result object into a User Administration object. For this reason, an attribute's mapping section defines how User Administration object attributes map into directory object attributes. This is pre-configured, but you can configure attributes at any time in order to better meet your organization’s needs.
Click Preview Data to verify how the objects are mapped.
Other Configuration
| Active | Activates/deactivates the directory configuration. |
|---|---|
| Use Node Referrals | Enables/disables the JNDI lookup java.naming.referral option. This option should be enabled for Active Directory servers configured without a DNS. |
| Ignore Communication Er... | Ignores/recognizes communication errors when Active Directory returns domain names for referrals other than the name specified in on the server. |
| Read Timeout (ms) | Choose a value to set how long Development Testing Platform should wait for a response before timing out. |
| Connection Timeout (ms) | Choose a value to set how long Development Testing Platform should wait when connecting to the server before timing out. |
| Environments | Field for entering JNDI environment properties in Java properties format. |
| Import Groups | Enables/disables queries to the server for group and group membership information. The Group Search Configuration and Membership Search Configuration sections appear if this option is enabled. |
Group Search Configuration
Group Search Configuration uses the same settings as User Search Configuration. Group Search does not, however, support the Preview Data function.
Membership Search Configuration
Configure these settings to control how DTP establishes the correlation between LDAP users and LDAP groups.
Synchronizing Group Membership Based on User Information
Disable the Use Membership Attribute option (default) to allow DTP to determine group membership based on user information.
\
When a user logs into DTP for the first time, the following process occurs:
- Groups the user is a member of are retrieved from the server
- If groups don’t already exist, equivalent DTP groups are created
- The user is associated with the created DTP groups.
Groups cannot be synchronized individually. Options for this mode are similar to the User Search Configuration and Group Search Configuration options. See User Search Configuration for additional information.
Synchronizing Group Membership Based on Group Information
Enable the Use Member Attribute option to allow DTP to use the group information to determine possible members.
DTP will not automatically create DTP groups in this mode, but it will allow existing groups to be individually synchronized. The following settings are available:
| Group Member Attribute | Defines the directory object attribute key used to declare group members. |
|---|---|
| Member Attribute is DN | Enable or disable to a allow or deny the value in the Group Member Attribute field to be treated as a distinguished name. Disable this option to treat the value as a user login name or group name. |
| Enable Nested Groups | Enable or disable to allow or deny a group to be declared as a member of another group. |
Support for Active Directory Primary Groups
You can enable DTP to use Primary Group(s) on the Active Directory server:
- Open the $DTP_HOME\conf\PSTSecConfig.xml configuration file in an editor (the file and location are the same for Linux and Windows).
- Set the
<use-primary-groups>element totrue. This element is a child of the<ldap>node. - Restart DTP service (see Stopping DTP Services and Starting DTP Services).
When set to true, user group membership will be taken from Primary Groups if defined in Active Directory, as well as from basic Active Directory groups.